When it comes to online privacy and security, many people are turning to secure operating systems such as Whonix and Tails. But which of these two is the better choice for you? In this blog post, we’ll take a look at the features and benefits of both Whonix and Tails in order to help you make the best decision for your needs.
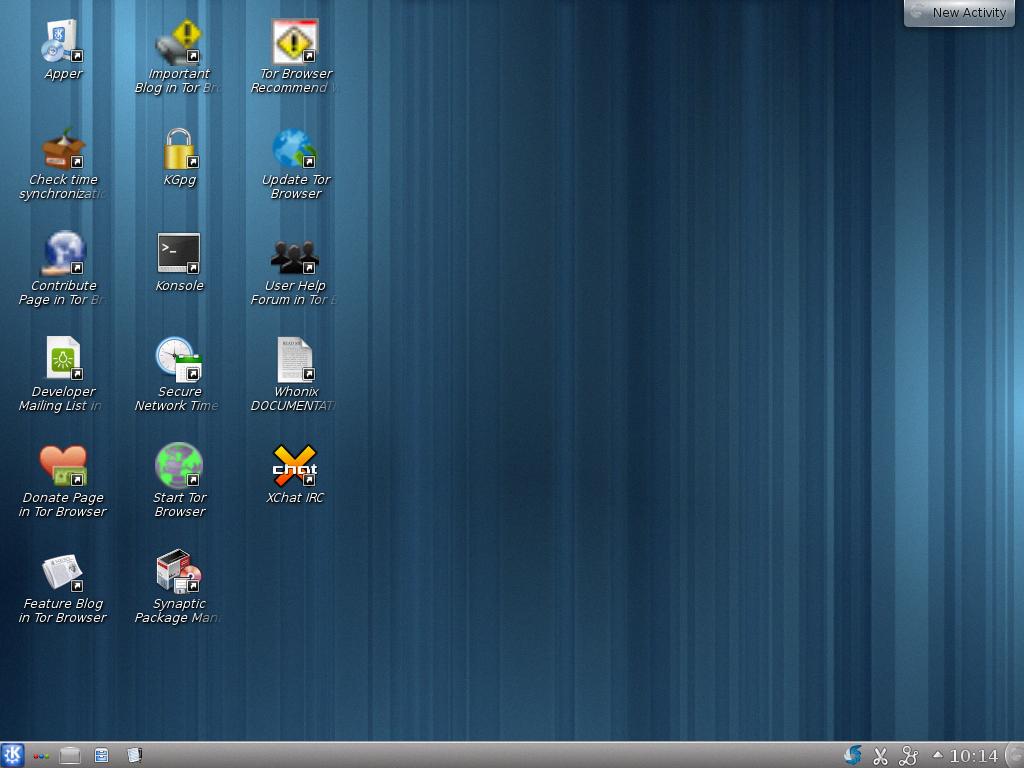
Whonix is a specialized operating system that is designed for maximum security. It works by routing all data packets through Tor, making it impossible for malicious actors to identify or trace your IP address. This added layer of protection makes Whonix an ideal choice for those who need extra security when accessing sensitive websites or files.
In addition, Whonix also provides users with an additional layer of protection against malware with root privileges. With this feature, even if a hacker was able to gain access to your machine, they would not be able to discover your real IP address or any other personal information.
On the other hand, Tails is a more general-purpose operating system that is designed for anonymous browsing and communication on the web. It does not include the same degree of protection as Whonix but still provides users with some degree of anonymity when using untrusted computers. However, since Tails does not provide the same level of protection against malicious actors as Whonix, it may not be suitable for those who need more robust security measures in place.
All in all, it can be said that while both Whonix and Tails have their own advantages and disadvantages, Whonix is generally considered to be a more secure option when compared with Tails due to its added layer of protection against malicious actors. Therefore, if you are looking for an extra level of security online then we recommend choosing Whonix over Tails.

Is Complete Anonymity Possible with Whonix?
Whonix is designed to offer users an anonymous experience when using the internet, but it is not completely anonymous. Whonix servers can be used anonymously over the Internet, and DNS leaks are impossible. However, malware with root privileges can still potentially discover a user’s real IP address. Additionally, other factors such as a user’s browser history and online activities can still be tracked by third parties. Therefore, while Whonix offers a high level of anonymity, it does not provide complete anonymity.
The Security of Tails Operating System
Yes, Tails is still secure. Tails is a live operating system that can be run directly from a USB drive or DVD on any computer without leaving any trace. It provides complete privacy and anonymity by routing all internet traffic through the Tor network and encrypting user data stored on the device. Additionally, it uses strong cryptographic algorithms to ensure data integrity and authenticity, making it impossible to tamper with. Finally, Tails also features an extensive set of security measures that prevent potential threats such as malware and keyloggers from compromising your data.
The Security of Whonix
Whonix is an extremely secure operating system, offering unparalleled privacy and anonymity for users. It works by routing all data packets through the Tor network, which encrypts the communication and helps to conceal your identity. This means that anyone attempting to attack you would only be able to reach the Whonix “Gateway” machine while leaving your “Workstation” machine completely safe and secure. In addition, Whonix makes use of isolation techniques to ensure that each component of the system runs in its own virtual environment, making it even more difficult for attackers to identify or infiltrate your system. All in all, Whonix provides an incredibly secure operating system that allows you to browse the internet without fear of being tracked or monitored.
Do I Need a VPN When Using Whonix?
No, a VPN is not required when using Whonix. Whonix provides advanced anonymity and privacy features out of the box and does not require a VPN for most users. VPNs can be used in combination with Whonix, but it’s important to understand if and why a VPN is needed in this context. A VPN can provide additional layers of security and privacy, but it also has the potential to interfere with the underlying protections that Whonix provides. Before using a VPN with Whonix, it is important to do some research to determine if a VPN will benefit or hinder your goals. Reading the Tunnels/Introduction wiki page is a great place to start as it provides an overview of how different types of tunnels interact with Whonix.
Can Internet Service Providers See What is Being Accessed Through Tails?
Yes, an Internet Service Provider (ISP) can see that you are using Tails. When you connect to the Tor network, your ISP and local network can detect that you are connecting to a Tor relay node. However, they cannot determine what you are doing or what kind of traffic you are sending or receiving. Tails take extra steps to protect your privacy by routing all of your traffic through the Tor network and encrypting it before it reaches its destination. This means that your ISP will not be able to see where your traffic is going or what kind of data is being sent over the internet.
Should I Use a VPN with Tails?
Yes, you should use a VPN if you use Tails. A VPN can help protect your privacy and security while using Tails by making it more difficult for third parties to track your activities online. It also helps to prevent eavesdropping and other forms of monitoring by masking your IP address and encrypting all the data that is sent over the internet. When choosing a VPN, it is important to pick one that is privacy-focused and reliable. Additionally, you should only use the VPN with Tails and never for any other purpose whatsoever in order to ensure maximum privacy protection.
Can Whonix Reveal My IP Address?
No, Whonix does not leak a user’s IP address or location while using Skype or other VoIP protocols. While it is difficult to anonymize voice over these channels, Whonix provides strong privacy and anonymity features that make it much harder for an adversary to track a user’s activities and location. Whonix achieves this through the use of Tor, which routes all traffic through multiple nodes in the Tor network before exiting onto the web, making it nearly impossible for any observer to know the source of the traffic. In addition, Whonix also includes various VPNs and other technologies that can further anonymize and protect a user’s activities.
Does Whonix Hide IP Addresses?
Yes, Whonix does hide IP addresses. It does this by routing data traffic through the Tor network, which anonymizes communication by encrypting it and bouncing it through multiple servers before it reaches its destination. This makes it extremely difficult for anyone to trace the origin of the data or its sender’s location.
How Much RAM is Required for Using Whonix?
For the best experience with Whonix-Workstation ™ Xfce, we recommend allocating at least 1024 MB of RAM. That said, you can run Whonix-Workstation ™ Xfce with as little as 512 MB RAM; however, during resource-intensive operations like upgrades, it is highly recommended that you allocate 1280 MB RAM to ensure that the virtual machine does not freeze.
Comparing the Safety of Tails and Whonix
It depends on what you mean by safer. Both Tails and Whonix route their traffic through the Tor Network, providing a high level of anonymity and privacy. However, Whonix is more secure when it comes to defending against a wider range of attack vectors. This includes protecting against malware, untrusted networks, and more. Ultimately, it depends on your threat model – if you need the highest level of defense against many different types of threats then Whonix might be better for you.
Source: kitploit.com
Can Whonix Be Run From USB?
Yes, you can run Whonix from a USB drive. To do so, you need to first select a suitable host operating system such as Ubuntu or Debian, then install it on your USB drive. After that is done, you can use the Whonix installation instructions to install it on your USB drive. The installation process will be slightly different depending on which operating system you choose. Once the installation is complete, you can boot up your computer with the USB connected and start using Whonix for secure and anonymous computing.
Does Whonix Use Tor?
Yes, Whonix does have Tor. Tor is the default networking application used by the Whonix operating system. It is a complete open-source anonymity system that provides users with privacy and security when browsing online. By using Tor, Whonix obscures the user’s IP address and other identifying information from anyone who might be monitoring their internet connection. This helps protect their identity and location while they are online. Additionally, Tor prevents websites from tracking the user’s activity and ensures that they remain anonymous while they are engaged in online activities such as browsing or downloading files.
Conclusion
In conclusion, both Whonix and Tails offer great advantages when it comes to protecting the user’s identity and data while online. Whonix provides a higher level of security due to its two-level architecture, which passes all data packets through the Tor system for anonymity. Additionally, if someone attempts to attack a user via Whonix, they will only be able to reach the ‘Gateway’ machine, leaving the other completely safe. On the other hand, Tails is an ideal solution for people who need to use an untrusted computer and want a secure environment in which to run applications safely. Overall, both solutions have their own merits and suit different needs depending on the user.