Secure Shell (SSH) is a protocol that provides a secure way to access and manage remote computers. It ensures that the communication between the client and the server is encrypted, protecting sensitive information from being intercepted by malicious actors. One essential component of SSH is the SSH key pair, consisting of a public key and a private key. The private key is kept on the client-side, while the public key is shared with the server.
To generate SSH key pairs, users often rely on tools like ssh-keygen, which is a command-line utility available on most Unix-like operating systems. While ssh-keygen is a powerful tool, it can be a bit complex for some users, especially those who are not familiar with the command line interface.
To simplify the process of generating SSH key pairs and enhance user experience, developers have created sshd keygen wrappers. These wrappers provide a graphical user interface (GUI) that makes it easier for users to generate SSH keys without the need for command line interaction.
One such example of an sshd keygen wrapper is the Mac’s built-in Remote Login feature. By enabling Remote Login in the Sharing preferences, Mac users can generate SSH key pairs effortlessly. This eliminates the need to use the command line and provides a more accessible option for users who prefer a graphical interface.
To set up Remote Login on a Mac, users need to access the System Preferences from the Apple menu. From there, they can navigate to the General settings and click on the Sharing option. In the Sharing preferences, users can enable Remote Login, which will allow them to generate SSH key pairs.
Once Remote Login is enabled, users can click on the Info button to access additional settings. Here, users can choose to allow full disk access for remote users if needed. This option grants Terminal, the command line interface on Mac, full disk access, ensuring seamless communication and access to protected areas like Mail, Messages, Safari, Home, and Time Machine.
For users who prefer more control over SSH key generation and want to explore additional features, third-party sshd keygen wrappers are also available. These wrappers often offer advanced options, customization capabilities, and additional security features. Users can find these wrappers by searching online or exploring software repositories specific to their operating system.
Sshd keygen wrappers provide an alternative to the command line interface for generating SSH key pairs. They offer a user-friendly and accessible way to enhance privacy and security when accessing remote computers via SSH. Whether using the built-in Remote Login feature on Mac or exploring third-party options, users can easily generate SSH keys and secure their remote connections.
What is SSHD Keygen Wrapper On a Mac?
The sshd keygen wrapper on a Mac is a tool that facilitates the generation of ssh secure shell keys for the purpose of privacy protection. It serves as a safeguard for remote access, allowing users to control and manage their connections securely.
Here are some key features and functions of the sshd keygen wrapper on a Mac:
1. Secure Shell (SSH) Protocol: The sshd keygen wrapper is specifically designed for Mac users who connect to their devices remotely using the SSH protocol. SSH ensures secure communication and data transfer between the local and remote systems.
2. Key Generation: The sshd keygen wrapper simplifies the process of generating SSH keys. These keys consist of a public key and a private key, which are used for authentication and encryption during the SSH connection.
3. Privacy Protection: By generating SSH keys, the sshd keygen wrapper enhances privacy and security. It allows users to establish encrypted connections, protecting their sensitive data from unauthorized access or interception.
4. Remote Access Control: With the sshd keygen wrapper, users can enable or disable remote access to their Mac. This gives them the ability to control who can connect to their system remotely, enhancing overall security.
The sshd keygen wrapper on a Mac is an essential tool for generating SSH keys, enabling secure remote access, and protecting privacy. It simplifies the process of establishing encrypted connections and allows users to have control over their remote access settings.
How to Enable SSH Full Disk Access On Mac?
To enable SSH full disk access on your Mac, follow these steps:
1. On your Mac, click on the Apple menu located in the top-left corner of the screen.
2. From the drop-down menu, select “System Preferences.”
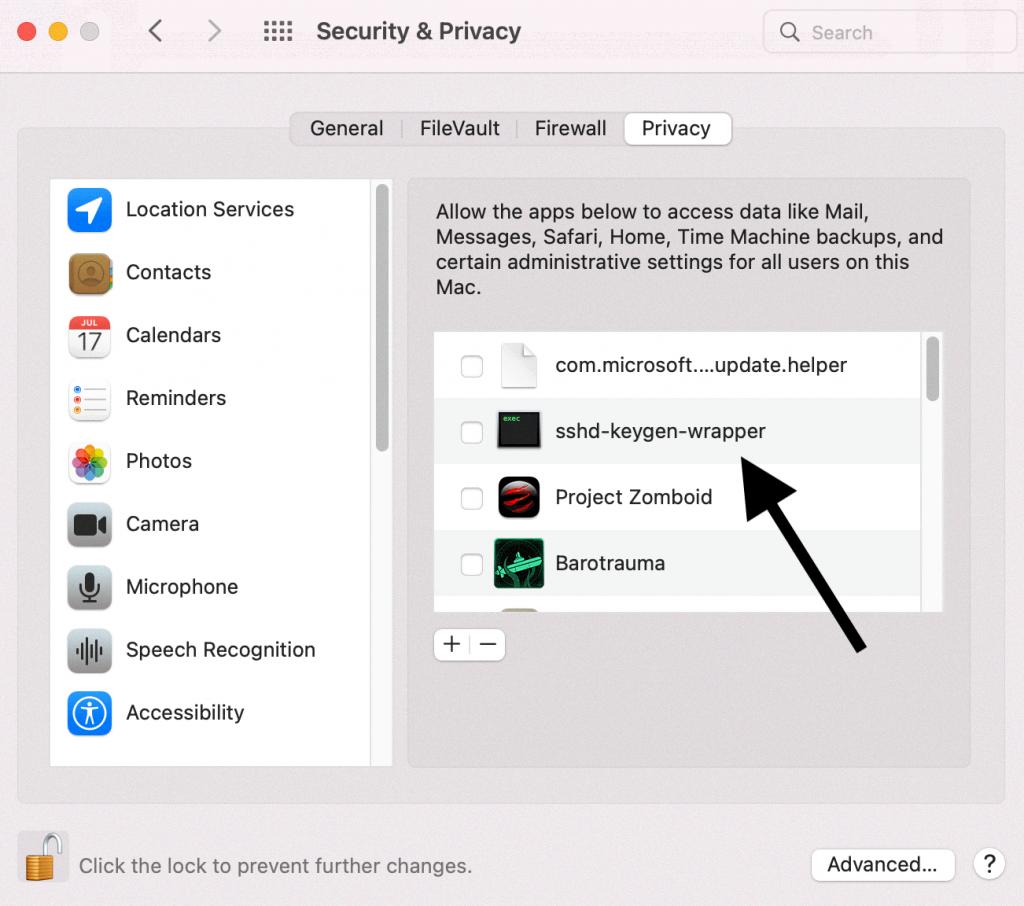
3. In the System Preferences window, click on the “Security & Privacy” icon.
4. In the Security & Privacy window, select the “Privacy” tab.
5. Scroll down and click on “Full Disk Access” in the left sidebar.
6. Click on the lock icon located at the bottom-left corner of the window to make changes.
7. Enter your administrator password when prompted.
8. Now, click on the “+” button below the list of apps to add a new app.
9. In the file picker dialog, navigate to the “/usr/sbin” directory.
10. Select the “sshd” file and click on the “Open” button.
11. The “sshd” file will now appear in the list of apps with full disk access.
12. Close the Security & Privacy window.
With these steps, you have successfully enabled SSH full disk access on your Mac. This allows remote users to have the necessary permissions to access your entire disk when using SSH.
What Should Have Full Disk Access On Mac?
To ensure optimal functionality and protection on your Mac, it is important to grant Full Disk Access permission to specific applications. These applications include Mail, Messages, Safari, Home, and Time Machine. Granting Full Disk Access permission allows these applications to access and modify data across your entire disk, providing enhanced functionality and convenience.
Here is a breakdown of why these applications require Full Disk Access:
1. Mail: Granting Full Disk Access to Mail enables the application to access and manage your email data seamlessly. It ensures smooth syncing, searching, and organizing of your emails, attachments, and other related data.
2. Messages: Full Disk Access permission for Messages allows the application to access and manage your message history, attachments, and other related data. This ensures smooth syncing and organization of your conversations across multiple devices.
3. Safari: Granting Full Disk Access to Safari enhances its ability to store website data, including cache files, cookies, and browsing history. This permission allows for efficient browsing and faster loading times, as well as seamless access to saved passwords and other website-related data.
4. Home: Full Disk Access permission for Home enables the Home app to securely store and access data related to your smart home devices. This includes information such as device configurations, automation settings, and user preferences, ensuring a seamless and secure smart home experience.
5. Time Machine: Granting Full Disk Access to Time Machine allows this backup utility to effectively and efficiently back up your entire disk, including system files, applications, and user data. This permission ensures comprehensive and reliable backups, protecting your valuable data in case of any unforeseen events.
By granting Full Disk Access permission to these specific applications, you are ensuring that they can function optimally and securely access the necessary data on your Mac. It is important to note that Full Disk Access should be granted judiciously, only to trusted applications that require it for their core functionality.
How Do You Give Terminal Full Disk Access?
To grant Terminal full disk access on macOS, follow these steps:
1. Click on the Apple icon located in the top left corner of your menu bar.
2. From the drop-down menu, select “System Preferences…”.
3. In the System Preferences window, click on the “Security & Privacy” icon.
4. Within the Security & Privacy preferences, click on the “Privacy” tab at the top.
5. Scroll through the sidebar on the left until you find and click on “Full Disk Access”.
6. To make changes, click on the lock icon in the bottom left corner of the window. You may need to enter your administrator password to unlock it.
7. Once unlocked, click on the “+” button located beneath the list of applications and files.
8. A standard Finder window will appear, allowing you to navigate through your system.
9. Locate and select the “Terminal” application, usually found in the “Utilities” folder within the “Applications” folder.
10. Click on “Open” to grant Terminal full disk access.
11. You should now see Terminal listed in the Full Disk Access window with a checkmark next to it, indicating it has been granted full disk access.
12. Close the System Preferences window.
By following these steps, you have successfully given Terminal full disk access on your macOS system.
Conclusion
The sshd keygen wrapper is an essential tool for ensuring privacy and security when connecting to a Mac remotely via the secure shell protocol (ssh). It provides a convenient way to generate ssh secure shell keys, which are necessary for establishing a secure connection. By enabling or disabling remote access, users have control over who can access their Mac remotely.
Setting up Remote Login on a Mac is a straightforward process that involves navigating to the System Settings, clicking on General, and then enabling Remote Login. Additional options, such as allowing full disk access for remote users, can be configured to enhance security.
Furthermore, the sshd keygen wrapper acts as a gatekeeper, granting full disk access permission to specific applications like Mail, Messages, Safari, Home, and Time Machine. This ensures that only authorized applications can access sensitive areas of the Mac, while other unauthorized applications are restricted from accessing them.
To grant Terminal full disk access in macOS, users can access the Security & Privacy settings in System Preferences. By navigating to the Privacy tab and selecting Full Disk Access, users can add Terminal to the list of applications with this permission.
The sshd keygen wrapper is a crucial component in maintaining privacy and security when connecting to a Mac remotely. It provides users with control over remote access and ensures that only authorized applications have the necessary permissions to access sensitive areas of the system.