Tunneling is an important component of Virtual Private Networks (VPNs) that allow users to securely access data over public networks. It works by encapsulating data as it moves through the internet, hiding it from other networks, and ensuring that only authorized users can access the data. In this blog post, we’ll discuss the basics of tunneling and how it works with VPNs.
At its core, tunneling is a process of encapsulating a packet within another packet so that the original packet can be transmitted across networks that don’t support its protocol. This process provides an encrypted connection between two nodes, allowing for secure communication over public networks. In order to establish a secure connection, tunneling protocols are used to set up and manage the VPN tunnel.
The most common tunneling protocols used in VPNs are Point-to-Point Tunneling Protocol (PPTP), Layer 2 Tunneling Protocol (L2TP), Secure Socket Tunneling Protocol (SSTP), and OpenVPN. Each protocol has its own advantages and disadvantages, but all use encryption to protect data during transit over public networks.
When using a VPN service, your computer sends out requests for data from various websites or services across the internet. The request is routed through an encrypted tunnel provided by your VPN service provider. All of your traffic is sent through this secure tunnel before being sent out on the open internet, making it impossible for anyone else to view or intercept your information without authorization.
The encryption used by a VPN service helps keep all of your online activities private and secure from hackers, government surveillance programs, or any other third party that may be monitoring your activity on public networks. By using a reputable VPN service provider with strong security protocols in place, you can rest assured knowing that all of your data will remain private while you browse the web or access services on public networks such as Wi-Fi hotspots or coffee shops.
tunneling is an essential component of Virtual Private Networks that helps keep your data safe while browsing online over public networks such as Wi-Fi hotspots or coffee shops. It works by encapsulating data as it moves through the internet and using strong encryption protocols to ensure that only authorized users can access the data being sent back and forth. By using a reputable VPN service provider with strong security protocols in place, you can rest assured knowing that all of your online activities will remain private while you browse the web or access services on public networks such as Wi-Fi hotspots or coffee shops.

Types of VPN Tunnels
1. IPsec Tunnels: IPsec tunnels are a type of virtual private network (VPN) tunnel used to securely connect two or more sites. They use Internet Protocol Security (IPsec) protocols, such as Authentication Header (AH) and Encapsulating Security Payload (ESP), to provide data encryption, integrity, and authentication. This makes them suitable for use in applications such as remote access, site-to-site connectivity, extranet access, and secure inter-office communication.
2. Dynamic Multi-Point VPNs (DMVPN): DMVPN is a type of VPN tunnel that provides dynamic connectivity between multiple sites over the Internet. It is designed to make it easier to set up and manage VPN connections, by allowing traffic between sites to be automatically routed through the most efficient path over the Internet. It also allows new sites to join the network without needing manual configuration of each device in the network.
3. MPLS-based L3VPNs: MPLS-based L3VPNs are a type of VPN tunnel that uses Multi-Protocol Label Switching (MPLS) technology for routing packets across multiple networks or sites connected over an IP network infrastructure. The MPLS labels provide information about how the packets should be forwarded within the network, making it possible for traffic from one site to another site to be sent through a secure tunnel without having to manually configure each device along the path. This type of VPN is often used when there are high-security requirements or when an organization needs a high level of performance and reliability from its network connections.
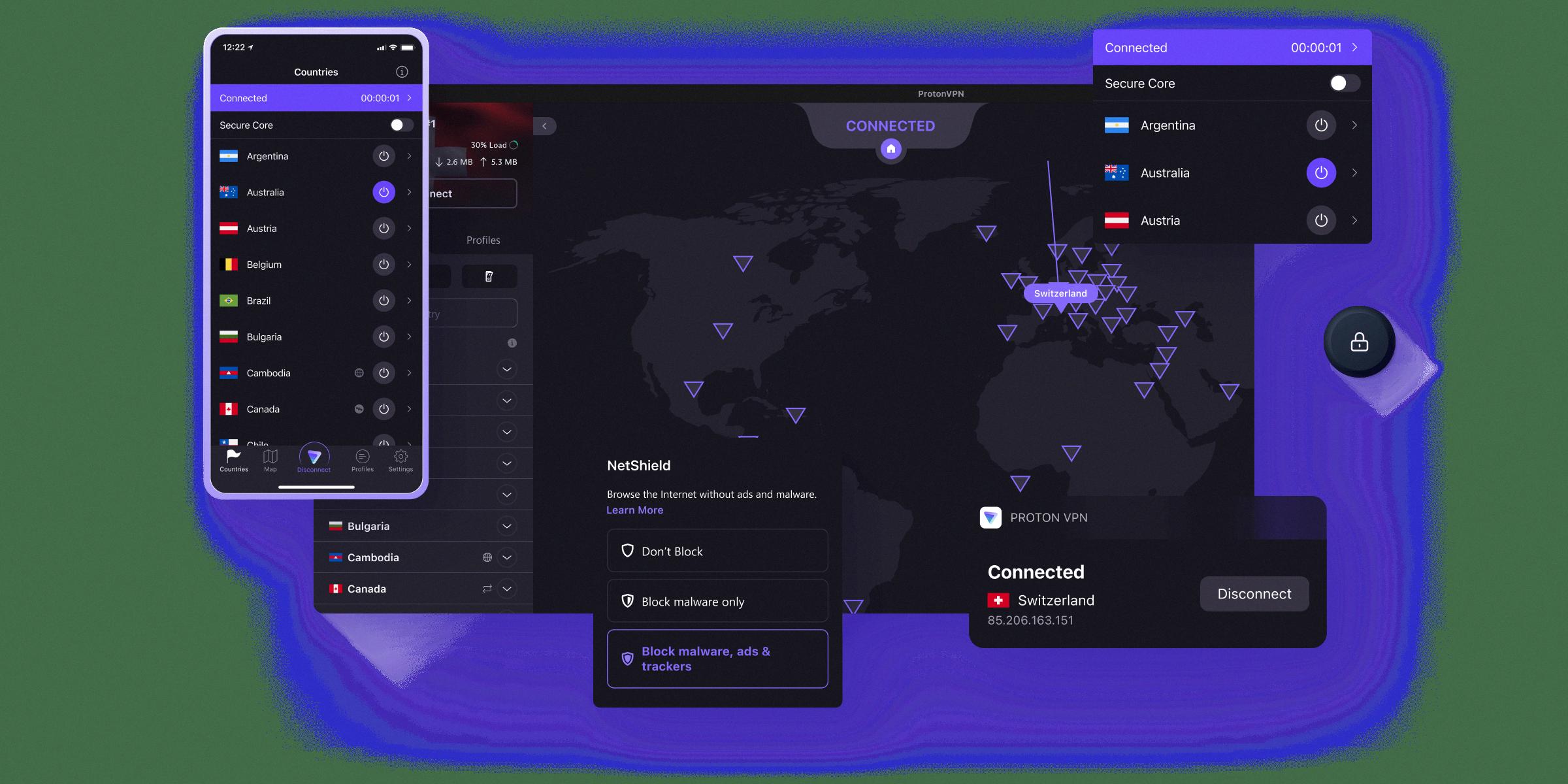
Source: protonvpn.com
Types of Tunneling in VPNs
The two main types of tunneling used in virtual private networks (VPNs) are point-to-point tunneling protocol (PPTP) and layer 2 tunneling protocol (L2TP). PPTP is a legacy protocol that has been around since Windows 95 and is still used today, although it is considered less secure than newer protocols. L2TP is a more secure option that uses IPsec for authentication and encryption. It is the preferred choice for businesses due to its ability to create multiple tunnels within an existing VPN connection, allowing for greater flexibility when configuring security settings. Both PPTP and L2TP are widely supported by most modern operating systems, making them suitable options for setting up a VPN.
Creating a VPN Tunnel
A VPN tunnel is created when a user connects to a Virtual Private Network (VPN) service. When the connection is made, the service will create an encrypted tunnel between the user’s device and the VPN server. This tunnel will allow for secure data transmission between both parties, without any external interference or tampering.
The encryption used by the VPN service is usually based on protocols such as PPTP, L2TP/IPSec, OpenVPN, or SSL/TLS. This encryption ensures that all data passing through the tunnel is securely encrypted and cannot be read by anyone outside the tunnel. Additionally, the service also provides users with a new IP address which hides their real IP address from third parties.
To ensure a secure connection, a user must use either an OpenVPN protocol or other security measures such as RSA encryption keys. Once connected to the VPN server, all of your online activities are now encrypted and safe from snooping eyes.

Source: cyberark.com
Advantages of VPN Tunnel Mode
VPN tunnel mode is a secure connection method that allows data to be sent between two endpoints over the Internet. The main advantage of tunnel mode is that it creates a virtual “tunnel” between two points, allowing all data passing through to remain encrypted and secure. This high level of encryption ensures that only authorized users can access the data and keeps it safe from outside intrusion. Additionally, tunnel mode provides a layer of authentication that helps to ensure the identity of both parties involved in the transmission. This authentication prevents malicious actors from intercepting or modifying any data that is sent through the tunnel.
The Most Secure VPN Tunneling Protocol
OpenVPN is widely considered the most secure VPN tunneling protocol available today. It uses 256-bit encryption as a default, but can also use other ciphers such as 3DES (triple data encryption standard), Blowfish, CAST-128, and AES (Advanced Encryption Standard). OpenVPN is an open-source protocol, meaning that it’s constantly updated and improved by developers to keep up with the latest security trends. It also offers an exceptional level of performance thanks to its ability to dynamically adjust the data transfer rate for optimal speeds. OpenVPN is compatible with multiple operating systems and devices, making it an ideal choice for users who are looking for a secure yet versatile VPN tunneling protocol.
Conclusion
In conclusion, tunneling VPNs are a great way to ensure privacy and security when you are connected to the Internet. They offer anonymity and encryption that keep your traffic and data secure from prying eyes, such as your ISP or hackers. There are several types of tunneling protocols available, such as PPTP, L2TP/IPsec, OpenVPN and SSTP, which each have their own advantages and disadvantages. It is important to research each one before selecting the best one for your needs. With tunneling VPNs, you can enjoy a secure connection that keeps your data and activities completely private.